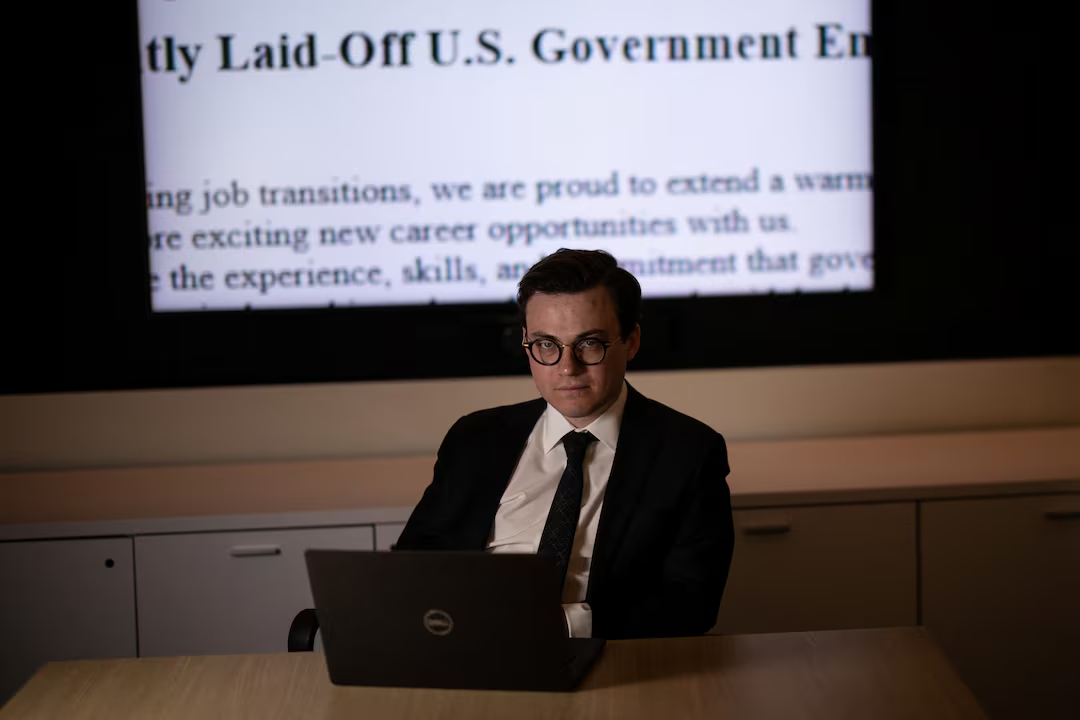
A network of companies allegedly operated by a Chinese tech firm has been targeting recently laid-off U.S. government employees, attempting to recruit them through job ads and fake consulting offers, according to research by Max Lesser, a senior analyst with the Foundation for Defense of Democracies. The campaign, which follows established tactics used in previous Chinese intelligence operations, raises concerns about espionage efforts aimed at exploiting vulnerable former federal workers.
Recruitment Efforts and Network Connections
Lesser’s research uncovered a network of four companies, which are said to be involved in a broader operation targeting ex-government workers and AI researchers. These companies, which have posted job listings on platforms such as Craigslist and LinkedIn, appear to be linked through overlapping websites, shared servers, and other digital connections. The four companies are also hosted on the same IP address as Smiao Intelligence, an internet services firm whose website went offline during the investigation.
Despite the efforts to track down these companies, Reuters faced numerous challenges, including dead-end phone calls, fake addresses, and deleted job listings. Lesser believes that the operation is designed to exploit the financial vulnerabilities of individuals affected by recent layoffs, including those initiated by the Department of Government Efficiency under President Donald Trump and tech tycoon Elon Musk.
The Potential for Espionage
Though it remains unclear whether the companies are directly linked to the Chinese government, analysts suggest that the network could serve as a vehicle for foreign-linked entities to gather sensitive information from former federal employees. Once recruited, these individuals could be asked to provide government-related intelligence or help expand the network by recruiting others.
The campaign’s focus on former government workers follows a pattern seen in previous espionage activities by both China and Russia, who have long targeted disgruntled or financially vulnerable U.S. employees to gain access to sensitive information. The FBI has warned that Chinese intelligence operatives have previously posed as academic institutions and recruitment firms to lure U.S. government employees into working as unwitting spies.
RiverMerge Strategies and Wavemax Innovation
One of the companies in the network, RiverMerge Strategies, described itself as a “geopolitical risk consulting” firm and posted job listings for positions such as “Geopolitical Consulting Advisor” and human resources specialists. Despite receiving over 200 applications for one of these roles, the company’s contact details were suspiciously linked to a Chinese phone number, and its physical addresses led to vacant or unrelated locations.
Another company, Wavemax Innovation, placed ads targeting laid-off government workers for positions in project management, research, and policy analysis. Similar to RiverMerge, Wavemax’s listed Singapore address led to a vacant field, raising further questions about its legitimacy.
Government Response and International Implications
In response to the investigation, a spokesperson for the Chinese Embassy denied any knowledge of the companies or their operations, emphasizing China’s commitment to respecting data privacy and security. Meanwhile, a White House spokesperson condemned such activities, underscoring the need for both current and former government employees to remain vigilant against foreign intelligence threats.
The FBI’s warnings and the tactics used in this case mirror earlier incidents, such as the 2020 conviction of Singaporean national Jun Wei Yeo, who worked as an agent of the Chinese government by luring U.S. government employees into espionage under the guise of consulting work.
Conclusion
This revelation highlights a growing trend of foreign intelligence services leveraging job recruitment scams to gain access to U.S. government insiders. As more employees are laid off due to restructuring or policy changes, they may become vulnerable to exploitation by foreign entities seeking to acquire sensitive information. The U.S. government has increasingly recognized the risks posed by such activities, urging employees to remain cautious about unsolicited job offers.